“Memblokir Port Virus di Mikrotik Menggunakan Firewall”
Daftar Isi
Pengantar
Penyebaran virus dan malware di jaringan dapat terjadi jika kita tidak selektif dalam mengaktifkan port apa saja yang digunakan. Untuk mengamankan jaringan dari penyebaran virus dan malware, kita dapat menutup port komunikasi yang tidak digunakan dan rentan dimanfaatkan oleh virus. Caranya dengan menggunakan rule firewall Mikrotik untuk men-drop paket yang masuk ke port yang tidak digunakan.
Memblokir Port Virus di Mikrotik Menggunakan Firewall
Caranya sangat mudah, silakan anda copy paste command berikut ini ke terminal Mikrotik :
/ ip firewall filter add chain=virus protocol=tcp dst-port=135-139 action=drop comment="Blaster Worm" add chain=virus protocol=udp dst-port=135-139 action=drop comment="Messenger Worm" add chain=virus protocol=tcp dst-port=445 action=drop comment="Blaster Worm" add chain=virus protocol=udp dst-port=445 action=drop comment="Blaster Worm" add chain=virus protocol=tcp dst-port=593 action=drop comment="________" add chain=virus protocol=tcp dst-port=1024-1030 action=drop comment="________" add chain=virus protocol=tcp dst-port=1080 action=drop comment="Drop MyDoom" add chain=virus protocol=tcp dst-port=1214 action=drop comment="________" add chain=virus protocol=tcp dst-port=1363 action=drop comment="ndm requester" add chain=virus protocol=tcp dst-port=1364 action=drop comment="ndm server" add chain=virus protocol=tcp dst-port=1368 action=drop comment="screen cast" add chain=virus protocol=tcp dst-port=1373 action=drop comment="hromgrafx" add chain=virus protocol=tcp dst-port=1377 action=drop comment="cichlid" add chain=virus protocol=tcp dst-port=2745 action=drop comment="Bagle Virus" add chain=virus protocol=tcp dst-port=2283 action=drop comment="Dumaru.Y" add chain=virus protocol=tcp dst-port=2535 action=drop comment="Beagle" add chain=virus protocol=tcp dst-port=2745 action=drop comment="Beagle.C-K" add chain=virus protocol=tcp dst-port=3127-3128 action=drop comment="MyDoom" add chain=virus protocol=tcp dst-port=3410 action=drop comment="Backdoor OptixPro" add chain=virus protocol=tcp dst-port=4444 action=drop comment="Worm" add chain=virus protocol=udp dst-port=4444 action=drop comment="Worm" add chain=virus protocol=tcp dst-port=5554 action=drop comment="Drop Sasser" add chain=virus protocol=tcp dst-port=8866 action=drop comment="Drop Beagle.B" add chain=virus protocol=tcp dst-port=9898 action=drop comment="Drop Dabber.A-B" add chain=virus protocol=tcp dst-port=10000 action=drop comment="Drop Dumaru.Y" add chain=virus protocol=tcp dst-port=10080 action=drop comment="Drop MyDoom.B" add chain=virus protocol=tcp dst-port=12345 action=drop comment="Drop NetBus" add chain=virus protocol=tcp dst-port=17300 action=drop comment="Drop Kuang2" add chain=virus protocol=tcp dst-port=27374 action=drop comment="Drop SubSeven" add chain=virus protocol=tcp dst-port=65506 action=drop comment="Drop PhatBot,Agobot, Gaobot" add chain=virus protocol=udp dst-port=12667 action=drop comment="Trinoo" disabled=no add chain=virus protocol=udp dst-port=27665 action=drop comment="Trinoo" disabled=no add chain=virus protocol=udp dst-port=31335 action=drop comment="Trinoo" disabled=no add chain=virus protocol=udp dst-port=27444 action=drop comment="Trinoo" disabled=no add chain=virus protocol=udp dst-port=34555 action=drop comment="Trinoo" disabled=no add chain=virus protocol=udp dst-port=35555 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=27444 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=27665 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=31335 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=31846 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=34555 action=drop comment="Trinoo" disabled=no add chain=virus protocol=tcp dst-port=35555 action=drop comment="Trinoo" disabled=no add action=drop chain=forward comment=";;Block W32.Kido - Conficker" disabled=no protocol=udp src-port=135-139,445 add action=drop chain=forward comment="" disabled=no dst-port=135-139,445 protocol=udp add action=drop chain=forward comment="" disabled=no protocol=tcp src-port=135-139,445,593 add action=drop chain=forward comment="" disabled=no dst-port=135-139,445,593 protocol=tcp add action=accept chain=input comment="Allow limited pings" disabled=no limit=50/5s,2 protocol=icmp add action=accept chain=input comment="" disabled=no limit=50/5s,2 protocol=icmp add action=drop chain=input comment="drop FTP Brute Forcers" disabled=no dst-port=21 protocol=tcp src-address-list=FTP_BlackList add action=drop chain=input comment="" disabled=no dst-port=21 protocol=tcp src-address-list=FTP_BlackList add action=accept chain=output comment="" content="530 Login incorrect" disabled=no dst-limit=1/1m,9,dst-address/1m protocol=tcp add action=add-dst-to-address-list address-list=FTP_BlackList address-list-timeout=1d chain=output comment="" content="530 Login incorrect" disabled=no protocol=tcp add action=drop chain=input comment="drop SSH&TELNET Brute Forcers" disabled=no dst-port=22-23 protocol=tcp src-address-list=IP_BlackList add action=add-src-to-address-list address-list=IP_BlackList address-list-timeout=1d chain=input comment="" connection-state=new disabled=no dst-port=22-23 protocol=tcp src-address-list=SSH_BlackList_3 add action=add-src-to-address-list address-list=SSH_BlackList_3 address-list-timeout=1m chain=input comment="" connection-state=new disabled=no dst-port=22-23 protocol=tcp src-address-list=SSH_BlackList_2 add action=add-src-to-address-list address-list=SSH_BlackList_2 address-list-timeout=1m chain=input comment="" connection-state=new disabled=no dst-port=22-23 protocol=tcp src-address-list=SSH_BlackList_1 add action=add-src-to-address-list address-list=SSH_BlackList_1 address-list-timeout=1m chain=input comment="" connection-state=new disabled=no dst-port=22-23 protocol=tcp add action=drop chain=input comment="drop port scanners" disabled=no src-address-list=port_scanners add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=fin,!syn,!rst,!psh,!ack,!urg add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=fin,syn add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=syn,rst add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=fin,psh,urg,!syn,!rst,!ack add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=fin,syn,rst,psh,ack,urg add action=add-src-to-address-list address-list=port_scanners address-list-timeout=2w chain=input comment="" disabled=no protocol=tcp tcp-flags=!fin,!syn,!rst,!psh,!ack,!urg
Hasil nya seperti berikut :
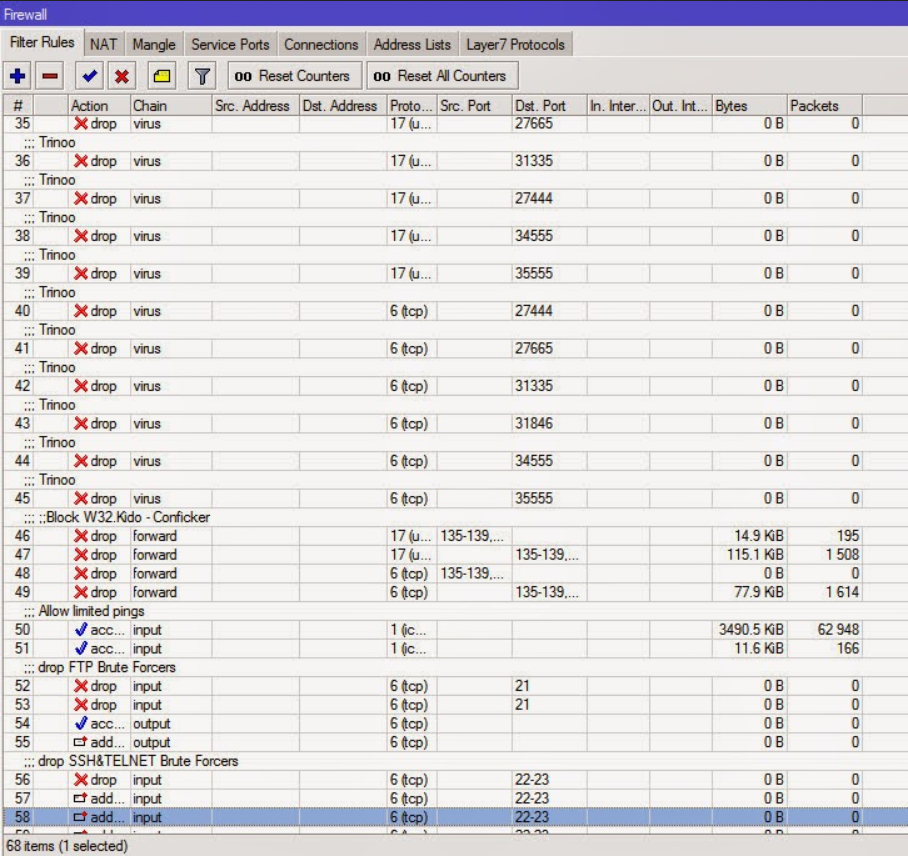
Sekarang kita sudah berhasil untuk bloking dari serangan Virus.
Sumber : https://mikrotikindo.blogspot.com/2014/03/memblokir-port-virus-di-mikrotik.html
Penutup
Sahabat Blog Learning & Doing demikianlah penjelasan mengenai Memblokir Port Virus di Mikrotik Menggunakan Firewall . Semoga Bermanfaat . Sampai ketemu lagi di postingan berikut nya.